Joomla! 3.0.0 ออกแล้ว
 ทีม Joomla! Project ได้ปล่อย Joomla! 3.0.0 ออกมาให้ได้ดาวน์โหลดกันแล้ว รุ่นนี้ เป็นรุ่นรองของรุ่นถัดไปของ Joomla CMS ซึ่งรุ่นนี้ เป็นรุ่นที่จะได้รับการสนับสนุนตามมาตรฐานปกติ Standard Term Support (STS) หรือจะเรียกกันตามประสาชาวบ้านอย่างเราๆ ก็คือ รุ่นใช้งานจริง แบบเก็บบั๊ก เพื่อเอาไปออกในรุ่นหลัก คือ 3.5 โดยการใช้งานจูมล่า 3.0 ผู้ใช้จะต้องวางแผนที่จะปรับปรุงให้เป็นรุ่นใหม่ที่จะออกในรอบของ STS คือ ทุกหกเดือน หรืออีก 6 เดือนถัดไป ก็จะมีจูมล่า 3.1 STS ออกมาอีก และก็ออกมาแค่ 6 เดือนเหมือนกัน ถึงจะออกเป็นรุ่น 3.5 อีกทีแบบใช้งานกันยาวๆ ประมาณเดือน เมษายนปีหน้าครับ ซึ่งคิดว่า การปรับปรุงไปใช้รุ่นนั้นจะทำได้ง่าย และรองรับการย้อนกลับของเวอร์ชันได้ด้วย
ทีม Joomla! Project ได้ปล่อย Joomla! 3.0.0 ออกมาให้ได้ดาวน์โหลดกันแล้ว รุ่นนี้ เป็นรุ่นรองของรุ่นถัดไปของ Joomla CMS ซึ่งรุ่นนี้ เป็นรุ่นที่จะได้รับการสนับสนุนตามมาตรฐานปกติ Standard Term Support (STS) หรือจะเรียกกันตามประสาชาวบ้านอย่างเราๆ ก็คือ รุ่นใช้งานจริง แบบเก็บบั๊ก เพื่อเอาไปออกในรุ่นหลัก คือ 3.5 โดยการใช้งานจูมล่า 3.0 ผู้ใช้จะต้องวางแผนที่จะปรับปรุงให้เป็นรุ่นใหม่ที่จะออกในรอบของ STS คือ ทุกหกเดือน หรืออีก 6 เดือนถัดไป ก็จะมีจูมล่า 3.1 STS ออกมาอีก และก็ออกมาแค่ 6 เดือนเหมือนกัน ถึงจะออกเป็นรุ่น 3.5 อีกทีแบบใช้งานกันยาวๆ ประมาณเดือน เมษายนปีหน้าครับ ซึ่งคิดว่า การปรับปรุงไปใช้รุ่นนั้นจะทำได้ง่าย และรองรับการย้อนกลับของเวอร์ชันได้ด้วย
ปล. ภายในตุลาคมนี้ ก็จะออกรุ่นแก้บั๊ก แล้วนะครับ
 ทีม Joomla! Project ได้ปล่อย Joomla 2.5.7 ออกมาให้ได้ใช้งานกันอีกแล้ว โดยรุ่นนี้แก้ไขปัญหาเรื่องความปลอดภัยครับ ซึ่งเป็นไปตามเป้าหมายที่ยิ่งใหญ่ของทีมผ่ายผลิต คือการให้ความช่วยเหลืออย่างสม่ำเสมอ เพื่อชุมชน Joomla. โดยท่านสามารถเรียนรู้เพิ่มเติมเกี่ยวกับ Joomla! Developement ที่
ทีม Joomla! Project ได้ปล่อย Joomla 2.5.7 ออกมาให้ได้ใช้งานกันอีกแล้ว โดยรุ่นนี้แก้ไขปัญหาเรื่องความปลอดภัยครับ ซึ่งเป็นไปตามเป้าหมายที่ยิ่งใหญ่ของทีมผ่ายผลิต คือการให้ความช่วยเหลืออย่างสม่ำเสมอ เพื่อชุมชน Joomla. โดยท่านสามารถเรียนรู้เพิ่มเติมเกี่ยวกับ Joomla! Developement ที่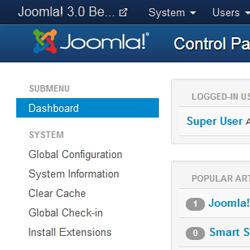 ทีม Joomla! Project ได้ปล่อย
ทีม Joomla! Project ได้ปล่อย